Reduce Risk and Minimize Effort with Vulnerability Mitigation
Published February 14, 2023 Last Updated on July 19, 2024

Better risk reduction. Less wasted effort. That’s what security leaders want and need when addressing IT security vulnerabilities. So how do we get there? Using risk-based mitigation.
The legacy all-in approach attempted to remediate every vulnerability discovered. By contrast, a risk-based approach prioritizes vulnerabilities according to the specific risk posed to the organization. Working through this ranked list ensures maximum risk reduction, so higher risk vulnerabilities get tackled first. It also provides better return on mitigation effort, so no effort is spent on lower risk vulnerabilities until the higher risk ones are fully addressed.
How to assess cybersecurity risk
This emphasis on prioritization is elegantly simple in theory – but how do we accurately assess risk? Risk is the combination of the probability of an event and its consequence. Applying this to IT vulnerabilities, we need to forecast the probability of a vulnerability being exploited, as well as the potential impact of its exploitation.
Thanks to the wealth of threat intelligence available, we can now assess the exploitability of any vulnerability. This includes examining repositories of known, exploited vulnerabilities, as well as following the development of exploit tools. Accurately assessing potential impact requires a thorough understanding of the environment. You need a business-centric view of an organization’s IT assets, with a clear mapping on how assets relate to each other and their importance to the overall business. Understanding likelihood and potential impact then serves as the base ingredients in the modern approach to mitigating vulnerabilities.
Operationalizing security
So, what’s been stopping us? As with many areas of security, the key challenge is in the operationalization of the different elements. In a perfect world, you’d remediate all IT vulnerabilities as soon as they’re disclosed, or at least put in place compensating controls. But in the real world, a host of obstacles get in the way.
One significant obstacle is the volume of new vulnerabilities. Recent years have seen the disclosure of over 20,000 new vulnerabilities. Multiply that out with the proliferation of devices in today’s IT environments, and you’ll see how organizations are often faced with hundreds of thousands, if not millions, of vulnerabilities to mitigate.
Another significant obstacle is the possibility of business interruption. Risk is directly proportional to business criticality, which is why the highest risk vulnerabilities tend to be on mission-critical systems. This often means limited windows to patch, more testing required, and all-around increased sensitivity to business interruption. The net result is often inaction. Security teams don’t get started because there’s much more than can be realistically done, and it’s unclear what matters most.
Managed Vulnerability Mitigation
Maximizing risk reduction while minimizing effort is at the heart of the value delivered by the new Ontinue add-on service: Managed Vulnerability Mitigation (MVM). MVM leverages Microsoft Defender for Endpoint (MDE) to discover vulnerabilities in the environment. Because customers of Ontinue ION already have the MDE agent deployed, no additional technology licenses or deployments are required.
The MVM service then uses a risk-based approach to surface the highest risk vulnerabilities discovered. These are often critical or high severity vulnerabilities, but could also include medium or even low severity vulnerabilities that pose a very specific risk to the environment, either because of high exploitability, high potential impact, or both.
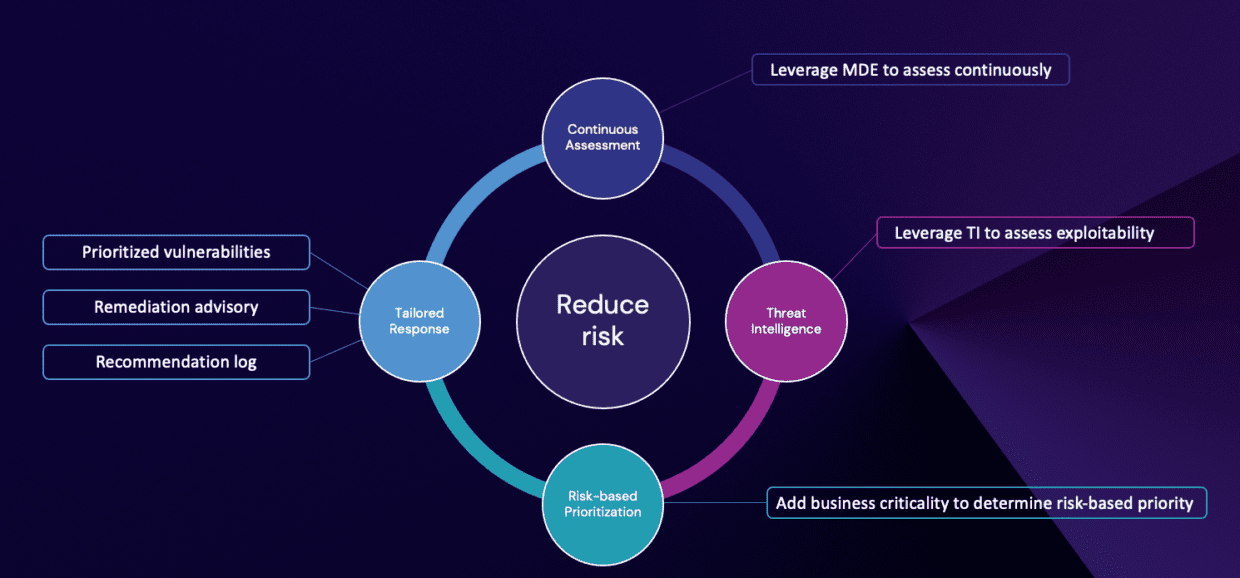
Thanks to MVM’s native integration with our ION service, the MVM service leverages ION’s deep knowledge of a customer’s environment to deliver superior risk prioritization. The monthly vulnerability reports list only the handful of vulnerabilities that carry most of the risk – instead of endless lists of assets and CVEs.
MVM also goes a step further beyond this focused list. The service also provides Remediation Advisory, where our Vulnerability Analysts provide direct technical support to customer IT teams on how to remediate. This includes fielding questions, delivering guidance on patching and compensating controls, analyzing false positives, and providing other ad-hoc advisory support for vulnerability mitigation. MVM also manages a recommendation log on behalf of customers, to systematically document risks that can’t mitigated.
Focus: The key to vulnerability mitigation
In our mission to mitigate vulnerabilities, it’s easy to get distracted with the latest zero-days and “celebrity” vulnerabilities. While these certainly pose a risk, the reality is threat actors are often exploiting run-of-the-mill vulnerabilities to breach organizations. Vulnerabilities that were clearly risky, given the ease in exploiting them and the systems where they reside, but never got addressed because of the overwhelming nature of the challenge.
MVM enables a new reality for customers: Rapid and effective operationalization of a vulnerability mitigation program, focused on the highest risk vulnerabilities, all with no additional licenses or technology. The end result? Greater security by focusing on the right things – not every thing.





