From Nation-State Threats to Agentic AI: Lessons from the Front Lines of Modern Security Operations
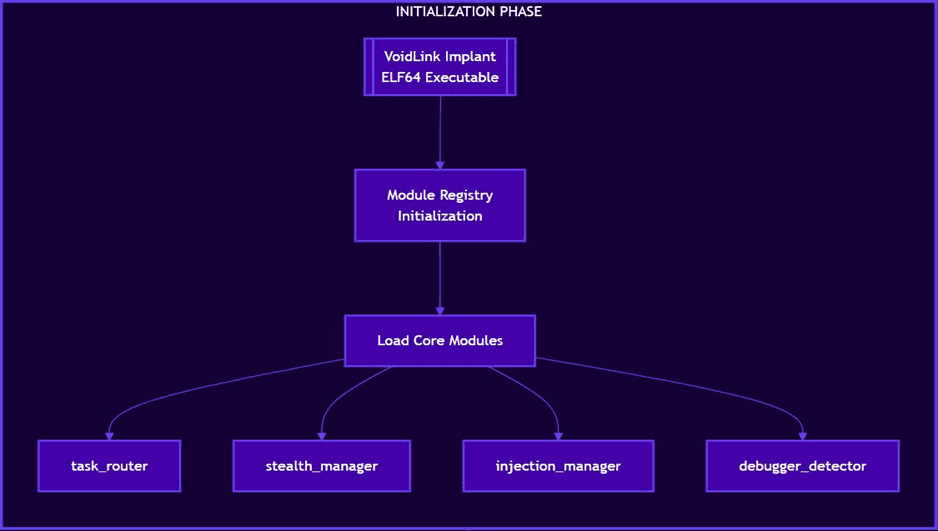
Craig, thank you again for joining, and thanks everybody, Ontinue customers and and friends of Ontinue who have joined. We’ve got a nice format here. We’ve got a fireside chat with Ontinue’s chief security officer, Craig Jones. We’ve got a few topics prepared, but we’ve also made time at the end for some questions and answers. So if you do have some questions for Craig as the conversation goes on, feel free to drop them in the q and a. We’ll try to address them as as the conversation goes on. But we like to keep it as interactive and informal as as we can, so it’s not a total lecture format. But first, I I think, Craig, thank you again for for doing this. Could you just tell us a little bit about yourself, your background in security, how you ended up at Ontinue, and and everything like that? Yeah. Sure. Hey, Rob. Great to meet you all. Obviously, as as Chris said, I’m I’m Craig Jones, the chief security officer here at Ontinue. Before I worked here, I worked for Sophos. So I was the senior director in charge of internal security operations for Sophos. Before that, I worked in various different places across the company in in security roles, including MDR. And one of the the jobs I had previously in Sophos was I commanded the whole of the Pacific Rim campaign. So if you’ve read any of this Sophos Pacific Rim print publications, those were all the outputs from the teams I led and and work that we did. And I’ll talk a little bit about that now because it’s pretty interesting. But as a whole, I love to speak. I’ve spoken multiple worldwide conferences, everything kinda globally, really. And recently, I just did a talk in b sides London on the China nexus and some of my experiences around dealing with, like, hardened Chinese APTs, which I’ll talk a little bit about in a second. And then on top of that then, though, I’ve worked in Ontinue actually, hilariously, three years today. I actually I joined Ontinue. Happy anniversary. Well, yeah. Thank you. More than anything, actually, I I joined Open Systems, which was the original payment company for Ontinue. And I joined Open Systems for a week, and then we branched out into Ontinue. So I had two jobs in a week, which is kind of funny and also definitely needs some explanation. You know? Thank you, Craig. Let’s let’s get into it. So and just, one other quick note just to orient everybody here. So a little bit of agenda. My fault. I should have gone through this at the beginning. We’ll go through Craig, thank you for providing your background. We will talk about the China Nexus campaign and, and some of your your experience with that. We’ll look look at some of the latest threat intelligence research coming out of the Ontinue advanced threat operations team. And then a topic that I know is is near and dear to your heart is how Ontinue’s security operations center, which you manage, is leveraging AI, which is pretty exciting. So, again, for for those of of you who have joined or joining late, if you have any questions, feel free to put them into the q and a. We wanna make this as interactive as possible. So with that, Craig, tell us about the the China Cyber Nexus attack Yeah. Sure. Experience with this. Yeah. Many thanks, Chris. So this is something that’s actually a huge interest of mine. I spent a long time in Sophos tracking down Chinese APTs, specifically ones that were using Sophos platforms and firewall platforms specifically to to use as, I I guess, gateways really into into networks. So we find from twenty twenty that there were various Chinese APTs using zero days against software firewalls. And they would use them in a way that was very quiet, that would basically go from initially, they they did a very wide campaign looking for access. And eventually, it got quieter and quieter and quieter and more, I guess, sneaky and more expensive for them. And we kinda find out that we were working against several EPTs. Now the reason we find this most really interesting is that they were using Sophos firewalls to actually develop the malware for Sophos firewalls. Now one of the really cool things we had back then was that we could actually run like an EDR type agent and get telemetry on what they were building and how. And over the course of, like, three years, we closely monitored around ten individuals in China that were building these Chinese Chinese tools, these tools for the the Chinese government. And we watched them build exploits. We watched them actually develop tooling for this. And then on top of that, we watched them eventually deploy it. So it was really clear that, you know, this is a really wide ecosystem. The people we were watching were really private companies working for kinda the MSS or the PLE, if you will. And we we kinda watched them develop these tools, and then in about six week cycle, these tools would pop up and actually be used. And I mean, it’s kinda fascinating for us watching which individual team built the tool, and then watching it appear then in in real life on a firewall in one of our customer environments, you know. And it was always really focused on like like Chinese interest. So really things like, you know, long term access, targeting of like edge devices, things like anti dissident operations. And we’d also find things like telecoms company banking and and things like like anything that had, like, large amounts of IP were something that was actually really targeted. But yeah. I mean, Chris, pop on the next slide for me. Thanks. Great. So this actually began, hilariously, in twenty twenty, right in the sick of COVID when the world was upside down. We got this crazy bug bounty request. We had a really wide bug bounty program. And we got external requesting that there was a a SQL I vulnerability in the software’s firewall. And this was new to us, like, to, you know, this platform had been tested and checked, but hearing like a SQL I vulnerability on this was just unheard of, you know. It kinda turned us upside down and and obviously, it was something of just like a huge interest. So we we got this bugbinding request and then we realized that the researcher claimed to be from Australia, but then the device they claimed to be testing on was actually in Shandong, China. And then we really realized over time that that was the epicenter of all the activity that we had. Now we ultimately ended up paying the researcher ten thousand dollars. Right? But we realized that this was actually one of these research companies double dipping. And that that’s a real common tactic for Chinese EPTs because this stuff is kinda built by an external company. You know, the researchers will also try and gain profit from it somehow as well. So imagine that. That happened on April twenty first. Literally like two days later, we we ended up with this crazy beginning of like a wide ranging campaign. And we we called it project Mexico internally, but the external name for it was Asner Rock. So this RCE was actually used against these Office firewall devices in a wide range. Now we ended up with around eighty thousand devices actually affected. So it was probably, you know, I’d hazard guess to say it was the world’s biggest instant response operation. We actually fought those APTs over the course of two days, built custom infrastructure to to take back control of the firewalls. And as well, we had a really cool mechanism in this office firewall, like internal updating format that allowed us to drop scripts to allow us to basically take back control. So one of the cool things we could do is actually drop scripts that would work as like an instant response script, allows us to kinda pull out some of the the attacker’s details, you know, pull out some of the files and scripts that they were using, and actually bring the firewall back into solid state, and and actually close out one of the one of the issues we had. Now I really encourage you to go and read about this. We we kind of wrote it all up as as the Pacific Rim campaign, but the initial incident was quite something because, again, it was around eighty eight thousand devices. It was actually way more in reality, but this was how many we managed to count from telemetry. The FBI published it as eighty eight thousand, so that’s a number I kinda go on. But again, it was a it was a crazy thing because they wide attack these firewalls. They run scripts on there that basically removed the, like, login details, any of the the kind of user information from their VPN logins, things like that, exfiltrate all into host in in the Netherlands, and then basically maintained access. Now what was interesting about it was that they actually messed up. So what should have happened is it should have run and just did all this super quietly, but they actually had a typo in the way that this way that this deployed and end up leaving a single artifact in the database, which was a clue as to how this worked, you know. So the initial report we had for this was actually through our service desk whereby some customers or partners were reporting that, hey, we’ve got this weird artifact appearing in the in the in the web UI, you know. We don’t understand where it’s come from. And then we worked out that actually it’s a it’s a remnant of a script that’s been run. And I think initially, we had about six or seven reports. So we didn’t think it was anything major. And I remember like coming in the morning and those six or seven reports were suddenly like hundreds of reports. And then as we started to get the telemetry in, we realized that this is actually a really wide ranging attack. So we we were kinda lucky that one, we had telemetry, and two, we had total command of these devices. You know, we kinda owned them soup to nuts, you know. That’s Craig, what does it feel like when you have that realization, that sort of dawning thing of this little attack that over eighty eight thousand yeah. I think it’s one of those aspects of, I think initially it’s just horror. I think anyone who’s been through like an incident like that, I’m sure there’s a few people laughing now, but in reality, was just pure horror. It was the thought of like, actually, we’ve got an unknown actor at this point having connected to these devices and exfiltrated credentials and they could get in and out any way they please. There’s nothing we can do right now to stop it. And it’s also on the edge of legality too. It took time for us to even work out if we have the legal capacity to be able to drop scripts on our customer devices to be able to fight these guys. And these are the kind of things that everyone says to have a battle plan and to think about your incident response plan. These are the things that you you can’t really guess as an incident response plan. And I I always think about the Mike Tyson quotes, you know, everyone’s got a plan until they’re punched in the face. And that was definitely us. Like we we had that moment of of really just having this huge punch in the face and you know, candidly too, it meant that we, you know, we had to be smart about what we’re doing. You know, I think all in all we had about fifty people working on the incident that, you know, I was commanding the middle of it. But we had some crazy stuff going on as well, where we built some infrastructure to to basically DDoS the attackers devices so that they could they would stop picking up the latest configs as our customers were changing configs, you know. So we built this crazy globally balanced DDoS system, which is nuts really from a security company building a DDoS system, you know. You know, it’s just the thing interference. Yeah. It was the only thing we could do until we got the hosting company to bring those systems down, you know, as in the attacker systems down. But yeah. I mean, so, you know, over the course of the period, we fought really hard over three days and we we managed to clean up all devices except for about four hundred or so. And to them, we took control of the domains involved in this. One was softwares firewall update dot com And we redirected them into sandbox or a sinkhole of ours in AWS. So it was a it was a it was quite a cool thing we managed to do in the end. We managed to keep them all interested. You know, keep them all kinda tied into our our infrastructure, and eventually, we managed to push an update down through the attackers’ update mechanism, which was kinda cool. One of the one of the I’ve a question for you. So sorry to interrupt. So three days you’re going through this, I have to imagine while you’re going through this, all of the APT attackers who have spent years of their lives executing this campaign, for them, it’s a very significant three days as well. Was there any, like, sign or signal, or did you did you have any sort of meeting your foes on the battleground experiences where you see, how they’re responding to the the sort of everything unraveling from their perspective? We did. We watched them actually change DNS quite a few times. So they tried to move their domains from different point them into different servers. As we started to do things to them, they realized that we were starting to pull this back. The other thing they did as well was try to use the the the same sequel I a few times on those devices. So it wasn’t just a single shot. They’re trying to use it again. Once they realized that we were pulling them out, they can run the campaign again to see if they could get back in and and try and get on top of us, you know. So we we we preempted that so by, you know, doing a quick patch of the the sequel live that was involved in this. And we also did things like we sync hold the attackers’ DNS on the devices themselves. So there’s quite a lot of quite a lot of things that we did to try and counteract it, but we did watch and try. They weren’t gonna let go easily. It was just quite something. But kinda going back to that, I mean, obviously, we had the initial bug bounty like like publication. And then see four days later, had this attack happen. Oh, sorry. Weekly, we had the attack happen. But we realized actually that it never occurred to us that bug bounty was related to this at the time. We just thought it was a kind of weird coincidence. So when we started to search for the the command that was left in the telemetry, we actually did a bunch of retro hunting. And luckily enough, we had about three months worth of data because weirdly, our product managers like to keep configuration data so they can work out which features are being used and how they’re configured and things like that. So they can decide how they’re gonna put their development funding into different areas. So we have all this configuration data that we could kinda hunt and mine through Splunk. And what we did, we went back over kind of three months and we realized that there’s one particular device in Chengdu that that were that was testing this command, had this command attribute in it about six weeks before the overall attack happened. Now what was kind of funny about that though was that we realized that this actually related back to a single person. Now this person had gone, they downloaded like a version of Sophos firewall x g. They had then checked out articles on the Sophos site. They’d registered themselves for like a like a forum username so that they could go and research a little more about the device. And they kinda done this with like a really with great opsec. It was hard to kinda tie them down. But what they’ve done is they’ve had great opsec, so like operational security. So they’ve hidden themselves very well. But what they’ve kinda done is when they registered the device, they were registered with a very anonymous email address. But when they were using the device in its configuration, they’d use their own personal email address, which allowed us to tie them back to an individual. So we we initially only seen, like, this device is kinda this ghost with real anonymous, you know, email addresses against it and other things. And then eventually, as we as we honed in, we found this individual researcher. Now, what was kinda cool about it is like he was in Shizuang Silent. Now, there’s a number of different companies in Chengdu that were kinda related to EPT forty one and few other EPT groups. Shizuan Silent is kinda there in the periphery, but Guan Tianfeng, the researcher involved in this who built this exploit and it was actually used in in this case, he he was believed to that company. He’d actually published other exploits and things in news groups. So it was really easy for us to actually tie him back and to tie him through the the kind of China nexus chain. The other cool thing as well is we could see that he was involved a lot in like external, like hacking competitions. And then we could actually attribute some of his associates with with other APT members that were well known and published by like other groups like Recorded Feature and things. So we got a really clear picture because of his kinda online personality, I guess. His his personal online footprint meant that we could actually find everything we needed about him, you know. So it was a really easy thing to go and talk to law enforcement about and and kinda tie the two pieces together. Well, Greg, I’m happy to share we have a special surprise guest today on the No. I’m just kidding. He wanted to join us to tell this side of the story. He’s thrilled with that actually. I’d love to question him. That would be fun, right? Yeah. Of course. So yeah. So you know, they ended up then with a kinda FBI like a, you know, indictment. And it kinda it kinda went a lot further. I mean, we find a lot of evidence around other attacks that he’d he’d orchestrated and built for, and it, you know, went went very far. I mean, the great thing about this inversely was that he had attacked the US, and the US government at the time were very for, you know, working through and trying to indict cyber criminals. Whereas if he’d just attacked other countries, like, if we wouldn’t have had anywhere near the amount of traction that we had here, being able to actually take it publicly. I think all in all, we had about six separate individuals that we’d find, but this was the only one we could talk about publicly because it’s the only one we could attribute to actual crimes that have, you know, we we got someone indicted for. So again, it was it was kinda super cool and, you know, it’s kinda, I guess, a slight inkling into the background that I’ve got. I mean, all in all, the Pacific Rim campaign, we had around forty incidents over the course of two years. I think that’s why I’m in my early forties and completely gray. I lost a lot of sleep for a number of years. But you can kinda read it all in the project mix sorry, the projects or Pacific Rim campaign publication. And, you know, I really applaud Sophos for for actually publishing it and being really open about it all. It’s an amazing story. Thank you for sharing that. And I we we will share as a follow-up to this. We’ll share that report out with everybody. It makes for fascinating reading. How about Craig, maybe switching gears on unless you wanna stay on this topic longer, we could talk about some of the, the research coming out of Ontinue’s advanced threat operations team and some of the, you know I know there was Rhys Downing recently wrote about, Linux c two framework that was being used for long term access, credential threat, theft and data exfiltration, and it was at least in part written with help from an LLM coding agent. So, yeah, tell tell us about some of the recent research coming out, maybe this particular one or, you know, what whatever’s most top of mind and exciting for you. Yeah. Sure. So yeah. I mean, Reese literally just published about this week. I really recommend, you know, for you to subscribe to our blog and, you know, keep keep a forefront of our blog, but we’re very lucky to continue. We have an advanced threat ops team, and if you’re a customer of ours, they’re your threat hunting team. So they’re the guys who are thinking about what new techniques are happening, what’s going on, and kinda building out, I guess, a a kinda wider threat hunt based on those tactics. Now, Void Link is a is a super cool piece. Reese has written a superb blog article of the the kind of depth of this, but effectively, it’s a a a stealth focused intrusion campaign that’s really characterized by, like, identity access. So it’s it doesn’t need much malware, but effectively, it it abuses cloud workflows to kinda evade like traditional detection models. So it very much focuses or prioritizes persistence through identity manipulation, session hijacking, and kind of privilege training really around Microsoft centric estates. But I mean, we we I mean, in Reese’s so he’s kind of found that, you know, researchers are now using AI. I’m gonna guess this anyway. Right? But they’re using AI to kind of vibe code new c two methods and also vibe code tools. So suddenly, the bar for entry for a lot of tools or quite extreme tooling has suddenly dropped. So traditionally, you’d have to be a a kinda elite hacker to be able to build tooling like this. And now, you know, it’s the likes of Claud AI and and other tools. It’s actually fairly accessible for anyone who has an idea and some inspiration. So I think this is really, I guess, the beginning of quite a wide ranging set of tools, you know. You know, this is obviously someone who really understands cloud environments and has used the likes of Clog to kinda build a tool that allows them to kinda exploit those. So it’s a it’s a really cool article, actually. I really recommend you to to to to to read it and to pick up on Reese’s work. We’ve had a ton of kind of feedback on it, and it’s been picked up by a number of different publications this week as well. So it’s it’s really gaining good traction. You know? Yeah. I’ll I’ll share that with everybody as a follow-up. And as a an another plug, look out at the end of this month. The advanced threat operation team is gonna be publishing its annual threat intelligence report. So that’s I we’ve been putting that out for the last few years, and that’s chock full of great information. And I’m sure we’ll be talking about the this this void link exploit and other other trends we’re seeing. And it makes a lot of sense that you see it really almost in every aspect of information life, this user adoption of of vibe coding as as you put it, Craig, and makes sense to you know, the the threat actors would be no exception to this as well. So maybe staying on that topic of AI, you you you and I were recently talking, and you were expressing some excitement about how the SOC is using AI. We’ve been using AI for a long time at Ontinue, you know, since we’ve since we’ve been a company, really. But over the last year, using Agentic AI to help with enrichment of investigating alerts and incidents. So can you tell me a little bit more about, you know, what you’re seeing and how we’re even starting to expose some of that to our customers? Yeah. Sure. So I mean, as you mentioned, Chris, we we’ve been using it for a long time. I mean, we were really on the age of the agentic SecOps journey, I guess. And it’s something that I’ve always been really quite interested in. Now we’re lucky in Ontinue that we have an amazing AI engineering team with they’re made from or they they kinda came from researchers from ETH and Zurich and, you know, they really understand their stuff. So so they can take what we need and really produce it into great AI workflows, you know, multiple agentic systems, you know, leveraging all of the newest and least AI tech, you know. So one of the things that we’re doing now is that we have We are I mean, obviously, use this thing in a day and day by day basis. I mean, this is our our kinda overall model as it stands. In reality, every single alert that comes into our SOC is investigate by AI now. Everything is done within kind of five minutes and we’re doing over fifty thousand checks a day. But effectively, we we’ve got like a cyber agent that goes it prioritizes, it builds a plan on what it’s gonna do, prepares an investigation. It actually goes through and investigates using a bunch of tools that we’ve built. So it can combine the tools that we have in our our automation platform to be able to answer questions for itself. It can then develop and actually pull together its response. And to that point, then it actually produces and communicates with the analyst. Now what we’ve been doing over the course of the last year and a half, I guess, is kinda really refining this to the point where in the next two weeks or so, in fact, VJ has just joined now who’s our our product marketing manager, we are looking to actually push this out to customers. So we can see the full back end, and I’ll I’ll dip it and maybe show you that in a second. But we’re actually gonna push in a view of this back end total for our customers too. So that’ll be available in the in our customer portal. So effectively, for every incident that comes through our our portal, our customers will actually benefit from from the AI tooling that we have running on every incident. So effectively, you know, we’ll give a preliminary AI analysis and it will run through what the AI’s thoughts are behind this this incident and and give you as a customer our kinda initial thoughts on it. And then every single alert that is followed up by automation and and the SOC itself, you know. So it’s just a great way of actually giving you, you know, some insight into what we see in the SOC itself with regards to AI too. I mean, it’s not quite the same as the our our overall AI assessment, which I’d love to show you, Chris, if that’s possible. Yeah. Please. Yeah. I’ll I’ll stop sharing here if you wanna share your screen. Yeah. That’d be great. Hopefully, you can see my screen. So here’s a little incident from Monteneu. Hopefully, you can all see it. Yep. Sorry. You’re you’re up there now. Oh, perfect. Sounds great. Yeah. So effectively, this is what we’ve got. So this is what our our cyber defenders work with every day. This is part of what makes us really unique, is that this this is our instant investigation report. Now every single incident is enriched like this. It doesn’t matter what it is. It doesn’t even matter if we haven’t seen that alert type before. Our system actually understands taxonomies. So for example, if it’s an alert that’s linked to identity, it understands that it needs to approach it from like an identity investigation path. What’s super cool about this though is we get as an analyst kind of the initial facts of what’s gonna happened here, the kind of breakdown of like the threat intelligence involved. It gives us situational awareness, so it will tell us if something has happened in this environment before, whether it’s kinda true positive or benign positive. We could see that this has happened thirty six times in this environment. It’s a benign positive. We get an idea of what might have actually triggered this environment. And that’s really based off of the that’s really based off of things we’ve seen in the environment previously, what we’ve trained the models to understand, and as well things that our analysts are aware of. And to that point then, what we have then is a kind of AI generated assessment of what’s actually happened and what’s actually happening here. Now what is kind of cool about this is that when we scroll down, this isn’t just a black box. So we we find all of the TI lookups, the I I and automation lookups, and as well all of the AI outputs that we’ve kinda worked to get with, you know. So for example, here, we can kinda see all of the outcomes, all of the searches and things that have been run. And in this case, for example, it’s a it’s a skill that looks at sign in attempts. So we see all of the sign in attempt details. So as a cyber defender here in Ontinue, it’s a really privileged place to be because we have a lot of our work preempted and pre done for us. Now, again, because it’s not black box, we can kinda see everything that’s gonna happen, what what’s going on, the account, whether it’s an, you know, account type, whether it’s a, you know, link to someone, the person who’s done this or, you know, the system will actually investigate and dig deeper in each piece, you know. So it’s actually a super cool piece to see. Now, for our customers, for you, we actually show in the activity log one second. Our pro preliminary AI analysis. So again, you know, we will give you what we see in a very summarized format so that you can make your own decisions quickly too. You know, we have multiple customers who kinda love to see these things happen and go through. And it also gives you a really clear example of our thinking and why we’ve come to certain conclusions, you know. It’s a combination of our AI doing investigation, our human analysts, on top of that are known knowns. So for example, as I showed you, you know, we we’re able to tell if something’s benign or not based on the probability of it happening with those entities previously in our in the environment. So it’s a really cool and privileged place to be to be able to see our our our kind of overall AI results, you know, especially the wider reports. And then the summarized reports then is a is a really cool kind of offshoot of that. You know? It Craig, we’ve got a for those who are not aware, we have a data science team that sits primarily in in Bern, Switzerland led by Theus Hossmann and Iris Safaka. What’s the feedback loop, and how does how how do your teams in the SOC work with Theus and Iris and team? Yeah. I mean, it’s a constant feedback loop, but if it’s effectively, we can give them feedback like this, and straight away we can just immediately feedback to that team whether something is good or not, and that gets pulled into their systems, and that feedback is pulled in and and updated and changed. So it’s a constant feedback loop. We’re quite lucky. The other thing we’ve done too is we we’ve got some analysts dedicated to AI now. So their principal job is to review these AI reports and actually feedback on them to the AI team. And so one of the best ways of making sure that we are constantly improving. Yeah. I I think it’s incredible. And the way I sort of understand it is, you know, if a SOC analyst gets an alert or an incident on their queue to work, it it sort of arrives to them already pre enriched, pre researched as though, like, a a tier one or tier two analyst had spent, you know, three hours already assembling all this information and correlating all this information and data for them. So pretty incredible. And we’ve been running this Agentic AI for over well over a year now. And I think what we’ve seen in the time that we’ve we’ve launched this is we’ve, reduced mean time to respond, and now we’re at a point where ninety nine point five percent of alerts that fire get resolved without ever being escalated to a customer. So pretty pretty incredible. Awesome. Well, thank you for sharing that, Craig. And, I do wanna mention and open it up to some questions and answers. I have a couple questions here, that that have come in that I can share. But but I also wanna encourage anybody who has questions to please chime in. So, Craig, my first question for you is, last week, Anthropic announced its new cloud model, which led to a three hundred billion dollar reduction in market cap for many software companies. What do you make of that? What do what impact do you see this is having on your team? I mean, obviously, we’ve been talking a lot about AI here. What impact do you see in in this in the near term for your team? And then, also, how does this affect, like, the threat landscape? And maybe it’s similar to what you were talking about earlier with the void link. Hey. I I think I think touching on the threat landscape first, I mean, I think these models are actually some of them are I mean, they’re supposed to have some elements of protection to stop people producing like this. It’s actually easily circumvented. So like, I think we’re gonna see more and more of kinda AI enriched malware. So that that aspect’s not going away. The part I think that is particularly interesting though for us is that we suddenly get more and more cyber aware models. You know, for example, the Anthropic model from last week, can kinda tie up more and more kind of cyber features. Now things that we’ve kinda done here whereby, you know, I was showing you earlier where it kinda gives you a couple of conclusions of what might have happened here. That’s actually really hard to do. And this anthropic model gets a little bit closer And I kinda see that aspect. Maybe it’s it’s it’s kinda lower lowering the the the the kind of bar for entry for that. You know? Hey, Craig. We’ve we’ve got a a question from the audience now here too. What’s the impact of these AgenTik AI features? I think the feature that you were just showing for Ontinue customers. Is there a way to play with these advanced features? I’m always looking for ways to play with the new AI than feature. Sure. So so we’re gonna turn on the the AI like, our early AI stuff to to you literally the next two weeks. Our preliminary AI analysis. It’s quite a mouthful though. But we’re gonna turn that on before long literally in the next two weeks. But you could speak to your cyber adviser, and we could turn it on almost immediately if you want to take a look at it. It’s not an issue at all. Good. Good. Thank you. So hopefully everybody caught that. If you are looking for early access, just reach out to your cyber adviser, and everybody should have access the next couple weeks. As for impact, we want you get to see what we see to some extent. It kinda gives you the enrichment that, you know, you’d only get from like another third party tool you’d have to purchase, but we we provide it as part of the service. And honestly, I think it’s quite a big boon. You know, I think it’s it’s a really useful addition to your kinda overall tool and and and product. I I I it is. Oh, and follow-up question. What about automation? Automation. Well, you still see our automation. I mean, all of our automation is published in the in our activity logs. So as it happens, if you’re looking for a custom automation, we might actually have some announcements on that this year fairly soon. So, yeah, stay tuned. Awesome. Alright. Great. Great. Okay. Thank you. Thank you. Thank you for that question. And one one one more question before we we kinda wrap up here. Something we’ve talked about, Craig, is the employee retention at Ontinue is unusually high, especially within the SOC. You know, for a job that I think can at a lot of companies be challenging, be a bit of a grind, You your team has a ninety six percent retention rate, which is incredible. What do you attribute that to? Yeah. That’s a good question, actually. Think it’s a number. Your blindingly brilliant leadership that’s good with it in this style. Well, yeah. Thank you. I think in reality, it comes down to several different things. I mean, it’s not a grind here. You know, we have tooling that actually makes these things fairly, you know, I wouldn’t say easy, but it makes makes life a little easier. We really listen to our analysts too. So their feedback on tooling, automation, outputs, detections, you know, we we take it on board. So I think if you’re an untenue analyst, I think you feel hard. I think that’s that’s pretty unique actually within many MSSPs, you know. We also have our teams involved in other projects. So they’re not just grinding on tickets all day. They’re involved in things like detection engineering, in automation, threat hunting. We have our AI teams, obviously. And, you know, some of their producing feedback for that summer, looking at run books in in our automation stacks. We’ve got a ton of things happening. I think that’s part of it too. It kinda keeps it all all interesting. Of the things we do as well, because we’re primarily remote, we have we try and get our teams together twice a year. So our our kind of SOC teams in the region. So for example, we just had our European team together in Porto last week. Think that’s really important. You know, when we’re all primarily remote, actually having a little bit connection really helps to kinda build the team and build team spirit and stuff. And I think small things like that all contribute and makes for a a wee happier environment. And, you know, when you get happy analysts, you got stable analysts. And then when you’ve got analysts who are stable, we know we don’t have this issue of, like, you know, quality and a slew of kinda, like, new analysts coming in all the time who kinda need to be massively trained every time. You know? We’re we’re I think we’re very privileged in the position. Yeah. Agreed. And we’re not burning them out because we follow take this follow the sun model approach, so they’re Yeah. Exactly. That was my other point. Obviously, kinda hoping that one was obvious. Yeah. I mean, we we only do follow the sun, so we don’t have any analysts working night shifts. It’s just days. So India hands over to Europe, who hands over to North America and Canada, back into India, Kings. So we end up in a a a situation where the guys are kinda working daytime only. So it’s it’s a way nicer working environment. Yeah. That’s excellent. Excellent. Hey, Craig. Thank you so much for the time today. We’ll we’ll wrap up here as follow ups for everybody. We will distribute the recording so you’ll be able to have access to this afterwards, And I will send out the, the China Cyber Nexus attack report from Craig and his time at Sophos. We’ll also share, Rhys Downing’s recent report into the VoidLink exploit. And, again, look for announcements coming soon about some of the automation features and exposing some of our, AgenTic AI capabilities, in your environment. So, again, thank you everybody for joining. That’s a wrap. And, Craig, thank you again for taking the time today.
Security does not usually change in clean, incremental steps. It changes in moments, often uncomfortable ones, when defenders are forced to adapt faster than their adversaries expect.
In a recent fireside chat, Craig Jones, Chief Security Officer at Ontinue, shared stories and insights from more than two decades in security operations. His experience includes tracking nation-state adversaries, responding to one of the largest firewall compromise campaigns ever observed, and building an AI-driven SOC designed for today’s threat landscape.
The conversation covered a wide range of ground, but three themes stood out clearly: how modern attacks really unfold, why identity and cloud are now the primary battlegrounds, and how AI, when used correctly, can fundamentally change security operations.
Nation-State Attacks Aren’t Loud; They’re Patient
One of the most striking parts of Craig’s story came from his time tracking Chinese advanced persistent threat activity targeting edge devices.
Contrary to the Hollywood version of cyberattacks, these campaigns were not flashy. They were quiet, deliberate, and deeply strategic.
The attackers focused on:
- Long-term access rather than immediate disruption
- Edge devices, particularly firewalls, as durable footholds
- Credential harvesting and persistence instead of destructive malware
In one campaign, attackers leveraged zero-day vulnerabilities in firewall software and quietly maintained access across tens of thousands of devices. What ultimately exposed the activity was not a dramatic alert. It was a single, small artifact left behind by a typo in a script.
That tiny mistake triggered a response effort that escalated into one of the largest coordinated incident response operations of its kind. The effort involved rapid infrastructure changes, custom remediation tooling, and constant counter-moves as attackers attempted to regain access.
The lesson is an important one for modern defenders. Today’s most dangerous attacks often look boring until they are not.
Identity Is the New Control Plane
As the discussion shifted from historical campaigns to current research, a consistent pattern emerged. Attackers are increasingly targeting identity and cloud workflows instead of traditional endpoints.
Recent threat research discussed in the webinar highlighted campaigns that:
- Use minimal malware or none at all
- Abuse legitimate cloud features and authentication flows
- Persist through session hijacking, token abuse, and privilege manipulation
This shift makes detection harder. When attackers behave normally inside cloud environments, traditional indicator-based approaches struggle to keep up.
From a defender’s perspective, this changes the game:
- You cannot rely on malware signatures alone
- Context matters more than volume
- Investigation speed becomes critical
This is where AI enters the picture.
What Agentic AI Actually Does in a Modern SOC
AI in security is often discussed in abstract terms. At Ontinue, it is operational.
Craig described how Ontinue’s SOC now uses agentic AI to investigate every alert that enters the environment automatically, consistently, and within minutes.
Instead of acting as a black box, the AI:
- Prioritizes alerts and builds investigation plans
- Gathers context from identity, endpoint, and cloud data
- Performs enrichment and historical analysis
- Produces a transparent assessment that analysts can review
Every alert arrives pre-investigated, with evidence, reasoning, and supporting data already assembled. Human analysts focus on judgment and decision-making rather than manual data gathering.
The result is faster response times, fewer false positives reaching customers, and analysts spending time on meaningful work instead of repetitive triage.
This is not AI replacing analysts. It is AI doing the work analysts should not have to do anymore.

Craig Jones
Chief Security Officer
Craig Jones oversees Ontinue’s global network of Security Operations Centers (SOCs). His role includes managing and optimizing the teams responsible for security monitoring, incident response, and threat detection across the company’s four SOCs. Previously, Craig was the Vice President of Security Operations at Ontinue. Before joining Ontinue, Craig spent eight years at Sophos, where he rose to Senior Director of Global Security Operations. At Sophos, Craig was responsible for the operational aspects of the company’s worldwide security program, ensuring that the organization’s global security infrastructure was robust and scalable.
Craig is a well-regarded expert in the field of cybersecurity, holding certifications such as GCIH and CISSP. He is actively involved in the cybersecurity community, volunteering as director of BSides Cymru/Wales since 2019 and frequently speaking at industry events. His thought leadership covers topics like incident response, SOC automation, threat intelligence, and SIEM. Craig earned a bachelor’s degree in Information Technology from the University of South Wales.