Attackers aren’t Breaking in Anymore, they’re Logging in
For years, cybersecurity has been built around a simple idea: keep attackers out.
Build stronger perimeters. Patch vulnerabilities. Detect malware. Stop intrusions before they happen.
But what if attackers don’t need to break in at all?
That’s the reality emerging from Ontinue’s 2H 2025 Threat Intelligence Report. Across thousands of investigations, one trend stood out above everything else: Attackers aren’t breaking in anymore, they’re logging in.
The Quiet Shift That Changes Everything
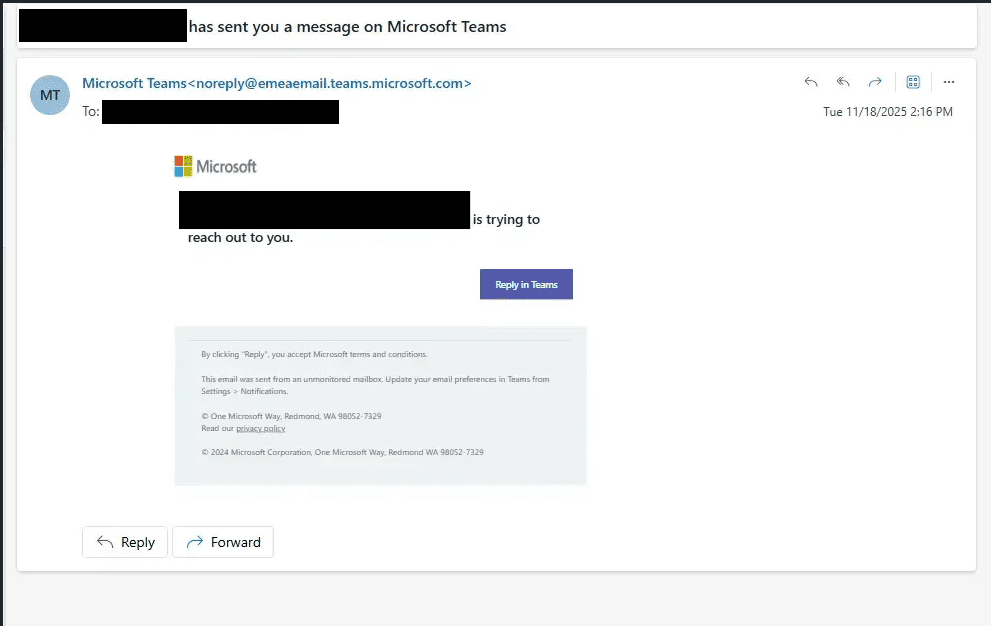
The most dangerous attacks today don’t look like attacks at all. There’s no exploit chain, no obvious malware beaconing, and no alarms triggered by a perimeter defense. Instead, what you see is something far more ordinary…a login. A valid username, a legitimate session token, a normal API call. From the system’s perspective, everything appears exactly as it should.
That’s precisely why this shift is so significant. Attackers are no longer forcing their way into environments, they’re entering through the front door, using credentials that grant them the same level of trust as legitimate users. In 2H 2025, identity became the primary attack surface. Techniques such as password spraying, adversary-in-the-middle phishing, OAuth abuse, and service principal compromise were no longer edge cases, they were the most common paths into modern environments.
Once inside, attackers didn’t behave like intruders. They behaved like users, blending into normal activity and operating within the boundaries of what systems are designed to allow.
The Rise of the Credential Economy
Behind this shift is something bigger than any single attack technique, it’s the emergence of an entire economy built around access. Infostealers, small but highly efficient pieces of malware, are quietly harvesting browser passwords, session cookies, and authentication tokens from infected machines. That data doesn’t just disappear; it is packaged, sold, and reused across a thriving underground marketplace.
This marketplace operates much like any other. If an attacker needs access to a corporate cloud environment, VPN credentials, or even an authenticated session that can bypass MFA, they don’t need to build it themselves – they can simply buy it. The barrier to entry has dropped dramatically.
The scale of this economy is growing rapidly. Listings of stolen credentials tied to the LummaC2 infostealer alone surged by 72%, highlighting just how quickly this model is expanding. This is no longer opportunistic hacking. It’s a system driven by supply and demand, where attackers increasingly choose the simplest and most efficient path: purchasing access instead of creating it.
Ransomware didn’t Go Away, it got Smarter
Ransomware remains one of the most disruptive threats organizations face. In 2025 alone, more than 7,000 ransomware attacks were reported, driven by a growing ecosystem of active threat groups. However, the real evolution isn’t in how ransomware executes, it’s in how it begins.
Today, ransomware rarely starts with an exploit. It starts with access, often purchased or stolen through the credential economy. Once inside an environment, attackers move quickly, escalating privileges, exfiltrating data, disrupting operations, and ultimately launching extortion campaigns.
That extortion has also evolved. Modern ransomware is no longer just about encrypting files. It’s a layered pressure strategy that combines data theft, operational disruption, and, in some cases, direct pressure on employees, customers, or partners. Even when organizations choose not to pay, the damage – financial, operational, and reputational – is often already done.
Trust Is Now the Attack Vector
One of the most striking findings in the report is how often attackers succeed without exploiting a vulnerability at all. Instead, they exploit trust; trust in OAuth integrations, SaaS platforms, automation pipelines, and developer workflows.
In one case, attackers abused OAuth tokens to gain access to more than 700 organizations without ever breaching the underlying platform. In another, a supply chain worm used stolen developer credentials to propagate malicious packages through CI/CD pipelines, effectively turning trusted automation into a distribution channel for compromise.
These incidents highlight a fundamental shift. Attackers are no longer limited to breaking systems, they are leveraging the very trust relationships that organizations depend on to operate. This isn’t an edge case. It’s a preview of how attacks scale in a cloud-first, interconnected world.
AI Is Lowering the Barrier, Not Raising the Ceiling
There has been no shortage of discussion about the role of AI in cybersecurity, but the reality emerging in 2H 2025 is more nuanced. Ontinue researchers observed early signs of LLM-assisted malware development – code that was clearly accelerated by generative AI.
What stood out wasn’t a leap in sophistication, but a shift in accessibility. The malware wasn’t autonomous or dramatically more advanced, but it was faster to build, easier to iterate, and more polished in appearance. AI is helping attackers move quicker and experiment more freely.
That’s the real change. AI isn’t yet creating fundamentally more dangerous attackers, it’s enabling more people to become attackers. By lowering the technical barrier to entry, it is expanding the pool of individuals capable of developing and deploying malicious tools.
The New Reality: Identity Is the Battlefield
If there is one defining takeaway from this report, it is that identity now sits at the center of cybersecurity. This extends far beyond traditional user accounts to include service principals, API keys, OAuth tokens, CI/CD identities, and machine-to-machine communication.
These identities collectively represent the new front doors into modern environments. They are how systems authenticate, how services interact, and how trust is established across platforms. When compromised, they provide attackers with legitimate access that is difficult to distinguish from normal activity.
In many cases, these identity layers remain insufficiently governed, creating opportunities for attackers to move freely once inside. As a result, identity is no longer just part of the security model, it is the battlefield itself.
What This Means for 2026
The organizations that will succeed in this new landscape will not necessarily be those with the strongest perimeters, but those that rethink how security is applied across identity. This means treating identity as the core control plane, monitoring authentication activity as closely as endpoint behavior, and securing both human and non-human identities with equal rigor.
It also requires a shift in mindset. Organizations must assume that credentials will be compromised at some point and design their defenses accordingly, focusing on rapid detection, validation, and response.
In a world where attackers log in instead of breaking in, the fundamental question has changed. It is no longer about whether attackers can gain access, but how quickly they can be detected and stopped once they do.
The Ontinue 2H 2025 Threat Intelligence Report provides a deeper look at the trends shaping today’s threat landscape, from identity-driven attacks and infostealer ecosystems to ransomware evolution and supply-chain compromise.