Alert volume reduction with ION Alert Tuning
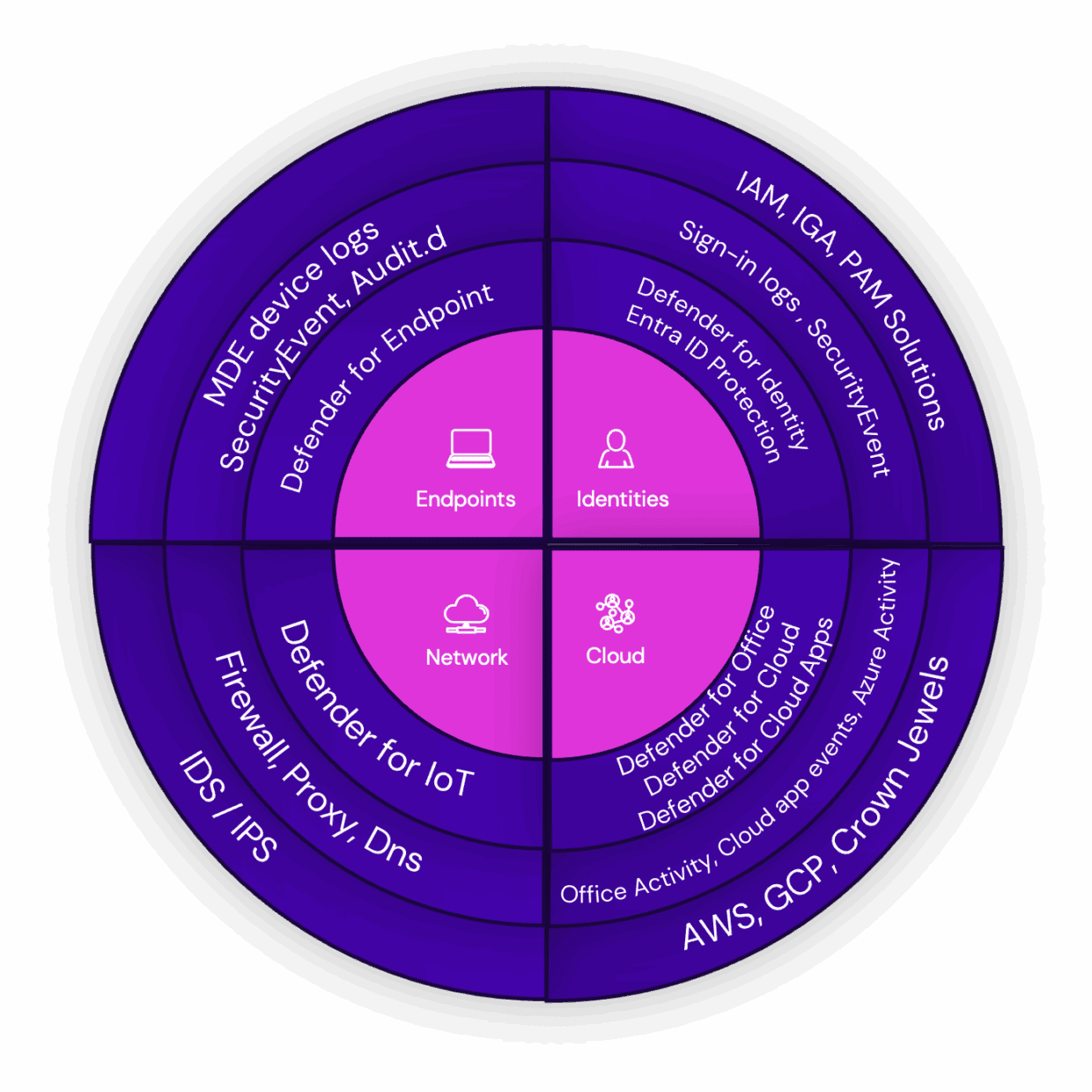
The ION Detection Stack is expanding rapidly, as our Threat Detection team continuously adds support for new data connectors and develops custom analytics rules for our use case library. We currently support over 60 data connectors, ranging from various solutions for SAP for our enterprise customers to Github for our customers in the software development industry, to name a few examples.
But as our detection coverage grows, so does the alert volume our Cyber Defense Center (CDC) has to process. While our detection quality framework “Triple-A” ensures high fidelity alerts are generated by the detection stack, additional mechanisms are required to reduce the alert volume and to ensure only relevant incidents populate the ticket queue of our Cyber Defenders. Keeping the queue free of incidents resulting from benign activity is key in improving operational efficiency and preventing alert fatigue or analyst burnout.
To learn more about how Ontinue prevents analyst burnout, visit our article: Understanding and Combating SOC Analyst Burnout
Tuning alerts during incident triage
The ION Alert Tuning component within our alert pipeline automatically triages alerts related to known benign activities that trigger our detection rules. These activities are commonly referred to in the industry as Benign Positives, Benign True Positives, or True Positives without Impact. They indicate that the detection logic is functioning correctly, and that tuning should occur during the triage process rather than within the detection logic itself.
Microsoft’s security products also offer capabilities for automatic alert triage. The features are known as Alert tuning in Defender XDR and Automation Rules in Sentinel. However, there are several key differentiators that set ION Alert Tuning apart from Microsoft’s native capabilities.
Transparency
We transparently report all tuning rules to our customers. Each tuning rule includes a reference to a ticket where the Cyber Defense Center documented how verdict of the investigation was reached. Depending on the Rules of Engagement (RoE), the customer’s approval for the tuning may also be included.
When a tuning action is applied to alerts that match a tuning rule, a tag is added to the corresponding incident in Sentinel. This incident contains the relevant alerts, and a comment specified by the CDC providing justification, creating an audit trail within the customer’s workspace.
All enabled tuning rules are reported on a monthly basis to our customers to provide full transparency.
Ease of use
As our Autonomous Investigator conducts a full investigation, before passing a detailed summary on to our Cyber Defenders, AI assisted ION IQ Insights automatically estimates the probability of the incident being a True Positive. This estimation is based on both historical data from the impacted customer and globally collected performance information about the alert signature. For incidents similar to those previously identified as benign, ION IQ Insights also proposes the appropriate conditions for tuning rules, automatically selecting the relevant entities from the incident.
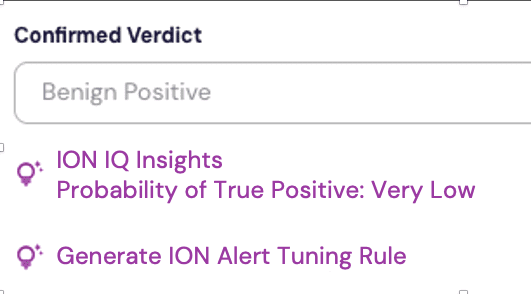
Together, the Autonomous Investigator, ION IQ Insights, ION Automate and ION Alert Tuning form the core of the Cyber Defender workbench, streamlining threat analysis, and enabling data-driven decision-making.
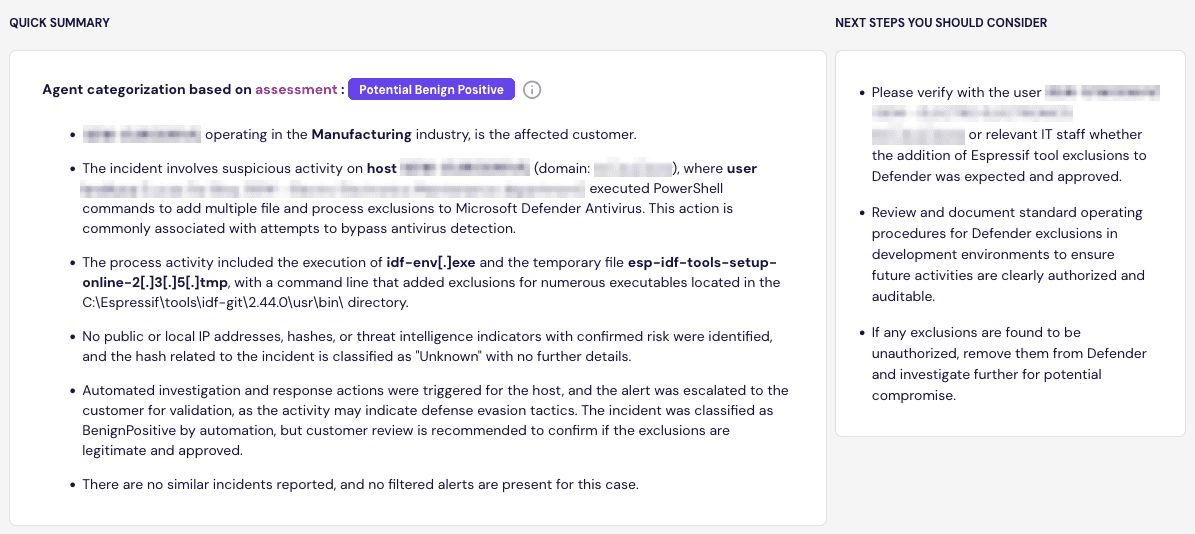
Autonomous Investigator passes a detailed investigation summary on to our Cyber Defenders.
Accuracy
The ability to accurately define which alerts are triaged automatically is paramount. A tuning rule that is too broad may create blind spots, where malicious activity is detected but triaged incorrectly.
At its core, a tuning rule in ION Alert Tuning matches alert names with entities such as host names, account names, or file names, similar to what Microsoft offers with Alert tuning and Automation Rules.
Analysts can craft complex tuning rules with conditions involving one or more alert names and entity types. For scalability, rules can contain lists of entities they match against, but they also support regular expressions. This allows the CDC to incorporate customer-specific naming conventions for hosts or accounts, or work with command lines that are similar but not identical, providing additional flexibility.
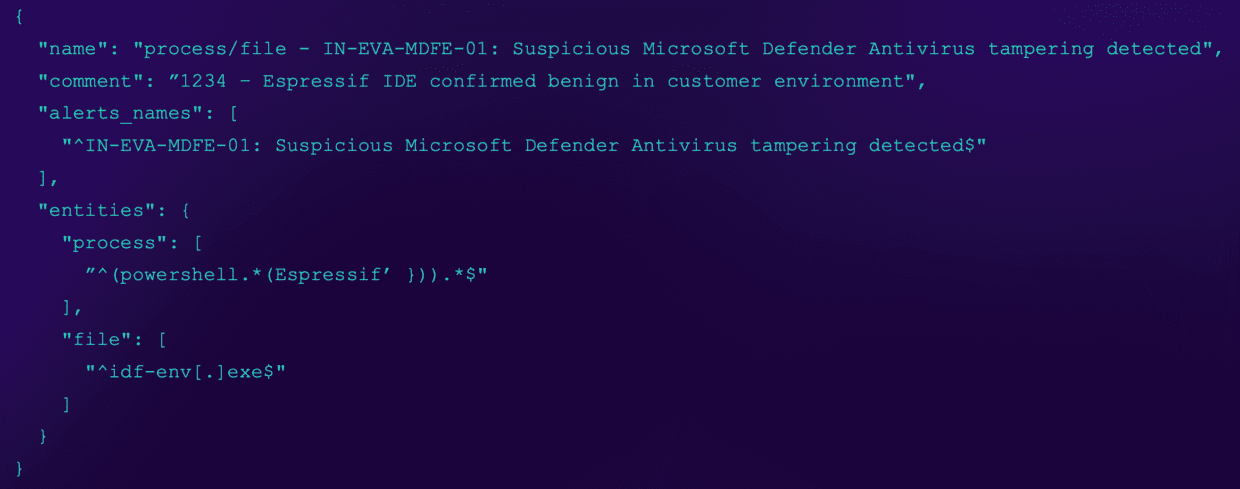
Visual representation of an ION Alert Tuning rule
Most tuning rules go into effect as soon as they are created. However, for planned maintenance work or security testing announced by our customers, we can define specific time periods during which a given rule should be active.
While triage actions such as incident closure or incident escalation are performed at the incident level, rule matching in ION Alert Tuning is applied at the alert level. This ensures that an incident is closed only when all alerts within it match a tuning rule. In all other cases, the incident is forwarded to the next component in the alert pipeline, ION Automate.
Scalability
As a component of our alert pipeline, ION Alert Tuning is strategically positioned between our customers Sentinel workspaces where alerts are generated and our Cyber Defenders’ ticketing tool. This placement allows tuning rules to be applied both at the individual customer level and on a global scale.
The latter is particularly useful when an EDR, IDS, or custom use case signature causes alert volumes to spike across all customers. These benign positive alerts are often caused by changes originating from operating system updates or software installations. In such cases, our Cyber Defenders step in quickly to prevent the ticket queue from becoming overwhelmed.
Conclusion
Benign activity can trigger detection signatures, resulting in alerts. Because the detection logic is correctly applied and the alerts are warranted, tuning should to be performed as part of the triage process rather than by updating the detection logic itself.
ION Alert Tuning is the component of the ION platform that delivers this functionality efficiently, automatically triaging more than 75% of incidents generated by the ION Detection Stack.
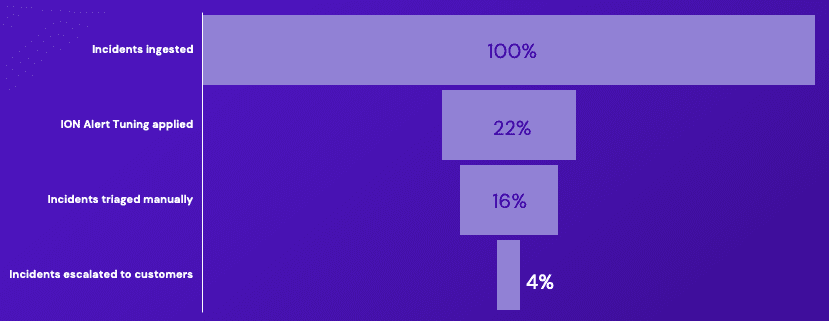
ION Alert Tuning reduces the number of incidents that require manual triage by more than 75%.
With ION Alert Tuning supporting the triage process, real threats are easier to identify for our Cyber Defenders, improving mean time to respond (MTTR).